User specific SSH Config File (/.ssh/config) You can create a user specific ssh configuration file per user on your Linux server. By default such client configuration file does not exist so you will need to create one depending upon your requirement. Create.ssh directory under user's home folder and assign 700 permission to this directory. I recently needed this but none of the options above worked, ssh -v showed that the command-line options passed via the -o switch were over-ridden by the values specified in my /.ssh/config file. What worked was this: ssh -F /dev/null @ From the ssh man page:-F configfile Specifies an alternative per-user configuration file. Oct 20, 2014 An SSH server can authenticate clients using a variety of different methods. The most basic of these is password authentication, which is easy to use, but not the most secure. Although passwords are sent to the server in a secure manner, they are generally not complex or long enough to be resistant to repeated, persistent attackers. No, it is not possible. The configuration options are described in the manual page for sshconfig and there is no such option as Pass. There are no patches (at least I didn't see any during the years yet), because it is very insecure to store passwords in plain text.
Some server providers, such as Amazon EC2 and Google Compute Engine, disable SSH password authentication by default. That is, you can only log in over SSH using public key authentication.
SFTP is a protocol that runs over SSH, so this means SFTP using passwords will not work by default when SSH password authentication is disabled.
To enable SSH password authentication, you must SSH in as root to edit this file:
Then, change the line
to
After making that change, restart the SSH service by running the following command as root:
Enable Logging In as root
Some providers also disable the ability to SSH in directly as root. In those cases, they created a different user for you that has sudo privileges (often named ubuntu). With that user, you can get a root shell by running the command:
If you instead want to be able to directly SSH in as root, again edit this file:
And change the line
to
After making that change, restart the SSH service by running the following command as root:
If you enable this setting, don't forget to set a strong password for root by running the command.
You can store and view the following security settings in the running-config file associated with the current software image by entering the include-credentials command (formerly this information was stored only in internal flash memory):
Local manager and operator passwords and (optional) usernames that control access to a management session on the switch through the CLI, menu interface, or WebAgent.
SNMP security credentials used by network management stations to access a switch, including authentication and privacy passwords.
Port-access passwords and usernames used as 802.1X authentication credentials for access to the switch.
TACACS+ encryption keys used to encrypt packets and secure authentication sessions with TACACS+ servers keys.
RADIUS shared secret (encryption) keys used to encrypt packets and secure authentication sessions with RADIUS servers.
Secure Shell (SSH) public keys used to authenticate SSH clients that try to connect to the switch.
The benefits of including and saving security credentials in a configuration file are:
After making changes to security parameters in the running configuration, you can experiment with the new configuration and, if necessary, view the new security settings during the session. After verifying the configuration, you can then save it permanently by writing the settings to the startup-config file.
By permanently saving a switch security credentials in a configuration file, you can upload the file to a TFTP server or Xmodem host, and later download the file to the HP switches on which you want to use the same security settings without having to manually configure the settings (except for SNMPv3 user parameters) on each switch.
By storing different security settings in different files, you can test different security configurations when you first download a new software version that supports multiple configuration files, by changing the configuration file used when you reboot the switch.
For more information about how to experiment with, upload, download, and use configuration files with different software versions, see:
'Switch Memory and Configuration' in the Management and Configuration Guide.
Configuring password security.
Enabling the storage and display of security credentials
To enable the security settings, enter the include-credentials command.
Syntax:
[no] include-credentials [radius-tacacs-only|store-in-config]
Enables the inclusion and display of the currently configured manager and operator usernames and passwords, RADIUS shared secret keys, SNMP and 802.1X authenticator (port-access) security credentials, and SSH client public keys in the running configuration. (Earlier software releases store these security configuration settings only in internal flash memory and do not allow you to include and view them in the running-config file.)
To view the currently configured security settings in the running configuration, enter one of the following commands:
show running-config: Displays the configuration settings in the current running-config file.write terminal: Displays the configuration settings in the current running-config file.
For more information, see “Switch Memory and Configuration” in the Basic Operation Guide.
To view the current status of include-credentials on the switch, enter show include-credentials. See Displaying the status of include-credentials.
The [no] form of the command disables only the display and copying of these security parameters from the running configuration, while the security settings remain active in the running configuration.
Default: The security credentials described in Security settings that can be saved are not stored in the running configuration.
| When executed with the The
|
| Stores passwords and SSH authorized keys in the configuration files. This happens automatically when |
| The |
The security settings that can be saved to a configuration file are:
Local manager and operator passwords and usernames
SNMP security credentials, including SNMPv1 community names and SNMPv3 usernames, authentication, and privacy settings
802.1X port-access passwords and usernames
TACACS+ encryption keys
RADIUS shared secret (encryption) keys
Public keys of SSH-enabled management stations that are used by the switch to authenticate SSH clients that try to connect to the switch
Executing include-credentials or include-credentials store-in-config
When include-credentials or include-credentials store-in-config is executed for the first time (for example, on a new switch) or when you have successfully executed the no include-credentials store-in-config command, the passwords and SSH keys are not currently stored in the configuration file (not activated). The following example shows the caution message displayed.
This caution message can also appear if you have successfully executed the [no] include-credentials store-in-config command.
The [no]include-credentials command disables include-credentials. Credentials continue to be stored in the active and inactive configurations, but are not displayed in the config file.
When [no]include-credentials is used with the store-in-config option, include-credentials is disabled and the credentials stored in the config files are removed. The switch is restored to its default state and only stores one set of operator/manager passwords and SSH keys.
If you choose to execute the [no]include-credentials store-in-config command, you are also presented with the option of setting new switch passwords.
You are queried about retaining the current SSH authorized keys on the switch. If you enter “y”, the currently active authorized key files are renamed to the pre-include-credentials names, for example:
All remaining authorized keys files with an extension are deleted.
The no include-credentials store-in-config messages and options
The information saved to the running-config file when the include-credentials command is entered includes:
password manager [user-name <name>] <hash-type> <pass-hash>
password operator [user-name <name>] <hash-type> <pass-hash>
where
<name> is an alphanumeric string for the user name assigned to the manager or operator.
<hash-type> indicates the type of hash algorithm used: SHA-1 or plain text.
<pass-hash> is the SHA-1 authentication protocol’s hash of the password or clear ASCII text.
For example, a manager username and password can be stored in a runningconfig file as follows:
Use the write memory command to save the password configurations in the startup-config file. The passwords take effect when the switch boots with the software version associated with that configuration file.
CAUTION: If a startup configuration file includes other security credentials, but does not contain a manager or operator password, the switch will not have password protection and can be accessed through Telnet or the serial port of the switch with full manager privileges. |
The password command has the following options:
Syntax:
[no] password <manager|operator|port-access> [user-name <name>] <hash-type> <password>
Set or clear a local username/password for a given access level.
| Configures access to the switch with manager-level privileges. |
| Configures access to the switch with operator-level privileges. |
| Configures access to the switch through 802.1X authentication with operator-level privileges. |
| The optional text string of the user name associated with the password. |
| Specifies the type of algorithm (if any) used to hash the password. Valid values are plaintext or sha-1. |
| The clear ASCII text string or SHA-1 hash of the password. |
You can enter a manager, operator, or 802.1X port-access password in clear ASCII text or hashed format. However, manager and operator passwords are displayed and saved in a configuration file only in hashed format; port-access passwords are displayed and saved only as plain ASCII text.
For more information about configuring local manager and operator passwords, see Configuring Username and Password Security.
For more information about configuring a port-access password for 802.1X client authentication, see 802.1X port-based access control.
SNMPv1 community names and write-access settings, and SNMPv3 usernames continue to be saved in the running configuration file even when you enter the include-credentials command.
In addition, the following SNMPv3 security parameters are also saved:
snmpv3 user “<name>'[auth <md5|sha> “<auth pass>'][priv “<priv-pass>']
Where
| The name of an SNMPv3 management station. |
| The (optional) authentication method used for the management station. |
| The hashed authentication password used with the configured authentication method. |
| The (optional) hashed privacy password used by a privacy protocol to encrypt SNMPv3 messages between the switch and the station. |
The following example shows the additional security credentials for SNMPv3 users that can be saved in a running-config file.
Although you can enter an SNMPv3 authentication or privacy password in either clear ASCII text or the SHA-1 hash of the password, the password is displayed and saved in a configuration file only in hashed format, as shown in the preceding example.
See “Configuring for Network Management Applications” in the Management and Configuration Guide for your switch for more information about the configuration of SNMP security parameters.
802.1X authenticator (port-access) credentials can be stored in a configuration file.
802.1X authenticator credentials are used by a port to authenticate supplicants requesting a point-to-point connection to the switch.
802.1X supplicant credentials are used by the switch to establish a point-to-point connection to a port on another 802.1X-aware switch.
Only 802.1X authenticator credentials are stored in a configuration file.
The local password configured with the password command is no longer accepted as an 802.1X authenticator credential. A new configuration command password port-access is introduced to configure the local operator username and password used as 802.1X authentication credentials for access to the switch.
The password port-access values are now configured separately from the manager and operator passwords configured with the password manager and password operator commands and used for management access to the switch. For information on the new password Command syntax, see Configuring password security.
After entering the complete password port-access command, the password is set. You are not prompted to enter the password a second time.
You can use TACACS+ servers to authenticate users who request access to a switch through Telnet (remote) or console (local) sessions. TACACS+ uses an authentication hierarchy consisting of:
Remote passwords assigned in a TACACS+ server
Local manager and operator passwords configured on the switch.
When you configure TACACS+, the switch first tries to contact a designated TACACS+ server for authentication services. If the switch fails to connect to any TACACS+ server, it defaults to its own locally assigned passwords for authentication control if it has been configured to do so.
For improved security, you can configure a global or server-specific encryption key that encrypts data in TACACS+ packets transmitted between a switch and a RADIUS server during authentication sessions. The key configured on the switch must match the encryption key configured in each TACACS+ server application. (The encryption key is sometimes referred to as “shared secret” or “secret” key.)
TACACS+ shared secret (encryption) keys can be saved in a configuration file by entering this command:
The option < is the encryption key (in clear text) used for secure communication with all or a specific TACACS+ server.keystring>
You can use RADIUS servers as the primary authentication method for users who request access to a switch through Telnet, SSH, console, or port access (802.1X). The shared secret key is a text string used to encrypt data in RADIUS packets transmitted between a switch and a RADIUS server during authentication sessions. Both the switch and the server have a copy of the key; the key is never transmitted across the network.
RADIUS shared secret (encryption) keys can be saved in a configuration file by entering this command:
The option < is the encryption key (in clear text) used for secure communication with all or a specific RADIUS server.keystring>
This option allows you to execute include-credentials for only RADIUS and TACACS. The radius-tacacs-only option does not cause the switch to store authentication passwords and SSH keys in the configuration file.
Syntax:
[no] include-credentials [radius-tacacs-only|store-in-config]
Enables the inclusion of passwords and security credentials in each configuration file when the file is saved onto a remote server or workstation. When [no]include-credentials is executed, include-credentials is disabled. Credentials continue to be stored in the active and inactive configuration files but are not displayed.
radius-tacacs-only:
When executed with the radius-tacacs-only option, only the RADIUS and TACACS security keys are included in the configuration when saving files remotely.
The radius-tacacs-only option can be disabled with either command:
store-in-config:
Stores passwords and SSH authorized keys in the configuration files. This happens automatically when include-credentials is enabled.
The [no] include-credentials store-in-config command disables the include-credentials command and removes credentials stored in the configuration files. The switch reverts to storing only a single set of passwords and SSH keys, regardless of which configuration file is booted.
When include-credentials radius-tacacs-only is executed, a warning message displays.
Caution message displayed for the radius-tacacs-only option
Secure Shell version 2 (SSHv2) is used by HP switches to provide remote access to SSH-enabled management stations. Although SSH provides Telnet-like functions, unlike Telnet, SSH provides encrypted, two-way authenticated transactions. SSH client public-key authentication is one of the types of authentication used.
Client public-key authentication uses one or more public keys (from clients) that must be stored on the switch. Only a client with a private key that matches a public key stored on the switch can gain access at the manager or operator level. For more information about how to configure and use SSH public keys to authenticate SSH clients that try to connect to the switch, see Configuring Secure Shell (SSH).
The SSH security credential that is stored in the running configuration file is configured with the ip ssh public-key command used to authenticate SSH clients for manager or operator access, along with the hashed content of each SSH client public key.
Syntax:
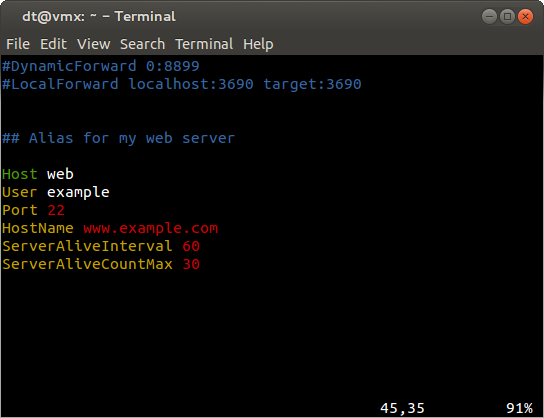
Ssh Config File Password Generator
Set a key for public-key authentication.
| Allows manager-level access using SSH public-key authentication. |
| Allows operator-level access using SSH public-key authentication. |
| A legal SSHv2 (RSA or DSA) public key. The text string for the public key must be a single quoted token. If the keystring contains double-quotes, it can be quoted with single quotes (
|
NOTE: The If you download a software configuration file that contains SSH client publickey configurations, the downloaded public keys overwrite any existing keys, as happens with any other configured values. |
To display the SSH public-key configurations (72 characters per line) stored in a configuration file, enter the show config or show running-config command. The following example shows the SSH public keys configured for manager access, along with the hashed content of each SSH client public key, that are stored in a configuration file.
SSH public keys
If a switch configuration contains multiple SSH client public keys, each public key is saved as a separate entry in the configuration file. You can configure up to 10 SSH client public keys on a switch.
The show include-credentials command provides the current status of include-credentials on the switch.
Syntax:
Displays information about the passwords and SSH keys stored in the configuration.
Stored in configuration — yes: | The passwords and SSH keys are stored in the configuration. Include-credentials was executed. |
Stored in configuration — no: | There is only one set of operator/manager passwords and one set of SSH keys for the switch. |
Enabled in active configuration: |
|
RADIUS/TACACS only: | Displayed when the option is configured. |
The following table shows the states of several access types when the factory default settings are in effect or when include-credentials is enabled or not enabled.
Switch storage states
| Type | Factory default | Include-credentials enabled | Include-credentials disabled but active | No include- credentials executed | |
|---|---|---|---|---|---|
Manager/Operator passwords & port access |
|
|
|
| |
SSH Public Key |
|
|
|
| |
SNMPv3 auth and priv |
|
|
| ||
RADIUS & TACACS keystrings | Not displayed in config | Same as Not displayed in config |
| ||
| |||||
CAUTION:
|
After you enter the
include-credentialscommand, the currently configured manager and operator usernames and passwords, RADIUS shared secret keys, SNMP and 802.1X authenticator (port-access) security credentials, and SSH client public keys are saved in the running configuration.Use the
no include-credentialscommand to disable the display and copying of these security parameters from the running configuration using theshow running-configandcopy running-configcommands without disabling the configured security settings on the switch.After you enter the
include-credentialscommand, you can toggle between the non-display and display of security credentials inshowandcopycommand output by alternately entering theno include-credentialsandinclude-credentialscommands.After you permanently save security configurations to the current startup-config file using the
write memorycommand, you can view and manage security settings with the following commands:show config: Displays the configuration settings in the current startup-config file.copy config <: Makes a local copy of an existing startup-config file by copying the contents of the startup-config file in one memory slot to a new startup-config file in another, empty memory slot.source-filename>config<target-filename>copy config tftp: Uploads a configuration file from the switch to a TFTP server.copy tftp config: Downloads a configuration file from a TFTP server to the switch.copy config xmodem: Uploads a configuration file from the switch to an Xmodem host.copy xmodem config: Downloads a configuration file from an Xmodem host to the switch.
For more information, see “Transferring startup-config files to or from a remote server” in the Management and Configuration Guide.
The switch can store up to three configuration files. Each configuration file contains its own security credentials and these security configurations can differ. It is the responsibility of the system administrator to ensure that the appropriate security credentials are contained in the configuration file that is loaded with each software image and that all security credentials in the file are supported.
If you have already enabled the storage of security credentials (including local manager and operator passwords) by entering the
include credentialscommand, thereset-on-clearoption is disabled. When you press the Clear button on the front panel, the manager and operator usernames and passwords are deleted from the running configuration. However, the switch does not reboot after the local passwords are erased. (Thereset-on-clearoption normally reboots the switch when you press the Clear button.)For more in formation, see Configuring front panel security.
The following restrictions apply when you enable security credentials to be stored in the running configuration with the include-credentials command:
The private keys of an SSH host cannot be stored in the running configuration. Only the public keys used to authenticate SSH clients can be stored. An SSH host's private key is only stored internally, for example, on the switch or on an SSH client device.
SNMPv3 security credentials saved to a configuration file on a switch cannot be used after downloading the file on a different switch. The SNMPv3 security replaceables in the file are only supported when loaded on the same switch for which they were configured. This is because when SNMPv3 security credentials are saved to a configuration file, they are saved with the engine ID of the switch as shown here:
If you download a configuration file with saved SNMPv3 security credentials on a switch, when the switch loads the file with the current software version the SNMPv3 engine ID value in the downloaded file must match the engine ID of the switch in order for the SNMPv3 users to be configured with the authentication and privacy passwords in the file. (To display the engine ID of a switch, enter the
show snmpv3 engine-idcommand. To configure authentication and privacy passwords for SNMPv3 users, enter thesnmpv3 usercommand.)If the engine ID in the saved SNMPv3 security settings in a downloaded configuration file does not match the engine ID of the switch:
The SNMPv3 users are configured, but without the authentication and privacy passwords. You must manually configure these passwords on the switch before the users can have SNMPv3 access with the privileges you want.
Only the
snmpv3 user< user_name> credentials from the SNMPv3 settings in a downloaded configuration file are loaded on the switch, for example:
Ssh Config File Example
You can store 802.1X authenticator (port access) credentials in a configuration file. However, 802.1X supplicant credentials cannot be stored.
The local operator password configured with the
passwordcommand is no longer accepted as an 802.1X authenticator credential. A new configuration commandpassword port-accessis introduced to configure the username and password used as 802.1X authentication credentials for access to the switch. You can store thepassword port-accessvalues in the running configuration file by using theinclude-credentialscommand.NOTE: The
password port-accessvalues are configured separately from local operator username and passwords configured with thepassword operatorcommand and used for management access to the switch. For more information about how to use thepassword port-accesscommand to configure operator passwords and usernames for 802.1X authentication, seeConfiguring Username and Password Security.
