- Microsoft Remote Desktop App Multiple Monitors
- Microsoft Remote Access App Ford
- Microsoft Remote Access Application
- Microsoft Remote Access Application
Microsoft has added a new feature to its 365 Apps which should make it easier to keep staff working even if they can't connect to the internet, plus another option for shared devices.
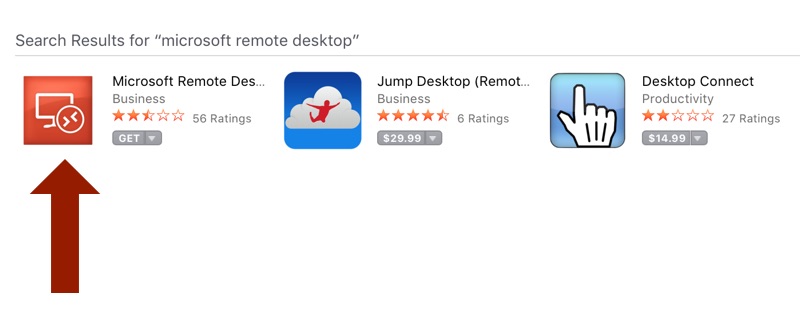
Windows 7 and early version of Windows 10. To configure your PC for remote access, download and run the Microsoft Remote Desktop Assistant. This assistant updates your system settings to enable remote access, ensures your computer is awake for connections, and checks that your firewall allows Remote Desktop connections. Windows Virtual Desktop on Microsoft Azure is a desktop and app virtualization service that runs on the cloud. Windows Virtual Desktop works across devices – including Windows, Mac, iOS, and Android – with full-featured apps that you can use to access remote desktops and apps.
Popular Searches
Microsoft's apps generally require customers' devices to connect to the internet at least once every 30 days to sign in to stay up to date. If the device does not connect to the internet in that time, the device's licensing token is not renewed and Microsoft's apps go in to 'reduced functionality mode' for that device.
Enterprise Software
While that's not a problem for many organizations with devices always connected to the internet, some industries have devices in the field or out at sea that might not connect for longer periods.
Microsoft Remote Desktop App Multiple Monitors
SEE: Office 365: A guide for tech and business leaders (free PDF) (TechRepublic)
It's easy to imagine technicians, engineers, scientists and others who spend months in remote areas where there is poor or no internet connectivity. Microsoft's new 'extended offline access' exception is for organizations supporting these workers.
'We're aware that in industries, including government, oil and gas, manufacturing, agriculture, and scientific research, some people work in secure or remote environments where they have limited or no internet connectivity for longer periods of time,' Microsoft notes in a blogpost.
Microsoft isn't getting rid of its 30-day login rule, but to remedy the situation for these specific sectors, it is introducing an exception that allows Microsoft 365 Apps to remain activated without the device connecting to the internet for up to 180 days.
'Workers in secure or remote environments who are offline for long periods of time can continue using Microsoft 365 Apps to stay productive on-the-job without worrying about being cut off from the tools they need most after 30 days,' Microsoft says.
This extended timeframe won't be available to all organizations. Microsoft explains in a footnote that 'eligible customers should contact their Microsoft account representative to determine if extended offline access for Microsoft 365 Apps for enterprise is the right solution for them'.
SEE: Microsoft is opening this 'advanced and sustainable' datacenter region next year
Via group policy, IT admins can enable extended offline access when the user installs Microsoft 365 Apps on a device.
For industries where shared devices are more common, such as healthcare, retail and in hospitality, Microsoft is also enabling device-based subscriptions for shared devices.
'Because the license is assigned to the device, workers aren't required to have their own Azure Active Directory identity. Workers can sign into the device as many times as needed and access all Microsoft 365 Apps, including Excel, OneNote, Outlook, PowerPoint, Publisher, and Word,' Microsoft explains.
Customers need to purchase 'the required number of Microsoft 365 licenses and assign a license to a device group in the Microsoft 365 admin center.'
Microsoft
Microsoft Remote Access App Ford
-->If your organization uses a remote access VPN solution, typically with VPN servers on the edge of your network and VPN clients installed on your users' devices, your users can use remote access VPN connections to access on-premises apps and servers. But you may need to optimize traffic to Microsoft 365 cloud-based services.
If your users do not use a VPN solution, you can use Azure Active Directory (Azure AD) Application Proxy and Azure Point-to-Site (P2S) VPN to provide access, depending on whether all your apps are web-based.
Here are the primary configurations for remote access:
- You are already using a remote access VPN solution.
- You are not using a remote access VPN solution and you want your remote workers to use their personal computers.
- You are not using a remote access VPN solution, you have hybrid identity, and you need remote access only to on-premises web-based apps.
- You are not using a remote access VPN solution and you need access to on-premises apps, some of which are not web-based.
See this flowchart for the remote access configuration options discussed in this article.
With remote access connections, you can also use Remote Desktop to connect your users to an on-premises PC. For example, a remote worker can use Remote Desktop to connect to the PC in their office from their Windows, iOS, or Android device. Once they are remotely connected, they can use it as if they were sitting in front of it.
Optimize performance for remote access VPN clients to Microsoft 365 cloud services
If your remote workers are using a traditional VPN client to obtain remote access to your organization network, verify that the VPN client has split tunneling support.
Without split tunneling, all of your remote work traffic gets sent across the VPN connection, where it must be forwarded to your organization’s edge devices, get processed, and then sent on the Internet.
Microsoft 365 traffic must take an indirect route through your organization, which could be forwarded to a Microsoft network entry point far away from the VPN client’s physical location. This indirect path adds latency to the network traffic and decreases overall performance.
With split tunneling, you can configure your VPN client to exclude specific types of traffic from being sent over the VPN connection to the organization network.
To optimize access to Microsoft 365 cloud resources, configure your split tunneling VPN clients to exclude traffic to the Optimize category Microsoft 365 endpoints over the VPN connection. For more information, see Office 365 endpoint categories. See this list of Optimize category endpoints.
Here is the resulting traffic flow, in which most of the traffic to Microsoft 365 cloud apps bypass the VPN connection.
This allows the VPN client to send and receive crucial Microsoft 365 cloud service traffic directly over the Internet and to the nearest entry point into the Microsoft network.
For more information and guidance, see Optimize Office 365 connectivity for remote users using VPN split tunneling.
Deploy remote access when all your apps are web apps and you have hybrid identity
If your remote workers are not using a traditional VPN client and your on-premises user accounts and groups are synchronized with Azure AD, you can use Azure AD Application Proxy to provide secure remote access for web-based applications hosted on on-premises servers. Web-based applications include SharePoint Server sites, Outlook Web Access servers, or any other web-based line of business applications.
Here are the components of Azure AD Application Proxy.
For more information, see this overview of Azure AD Application Proxy.
Note
Azure AD Application Proxy is not included with a Microsoft 365 subscription. You must pay for usage with a separate Azure subscription.
Deploy remote access when not all your apps are web apps
If your remote workers are not using a traditional VPN client and you have apps that are not web-based, you can use an Azure Point-to-Site (P2S) VPN.
A P2S VPN connection creates a secure connection from a remote worker’s device to your organization network through an Azure virtual network.
For more information, see this overview of P2S VPN.
Note
Azure P2S VPN is not included with a Microsoft 365 subscription. You must pay for usage with a separate Azure subscription.
Deploy Windows Virtual Desktop to provide remote access for remote workers using personal devices
To support remote workers who can only use their personal and unmanaged devices, use Windows Virtual Desktop in Azure to create and allocate virtual desktops for your users to use from home. Virtualized PCs can act just like PCs connected to your organization network.
For more information, see this overview of Windows Virtual Desktop.
Note
Windows Virtual Desktop is not included with a Microsoft 365 subscription. You must pay for usage with a separate Azure subscription.
Protect your Remote Desktop Services connections with the Remote Desktop Services Gateway
If you are using Remote Desktop Services (RDS) to allow employees to connect into Windows-based computers on your on-premises network, you should use a Microsoft Remote Desktop Services gateway in your edge network. The gateway uses Transport Layer Security (TLS) to encrypt traffic and prevents the on-premises computer hosting RDS from being directly exposed to the Internet.
See this article for more information.
Admin technical resources for remote access
Microsoft Remote Access Application
Results of Step 2
Microsoft Remote Access Application
After deployment of a remote access solution for your remote workers:

| Remote access configuration | Results |
|---|---|
| A remote access VPN solution is in place | You have configured your remote access VPN client for split tunneling and for the Optimize category of Microsoft 365 endpoints. |
| No remote access VPN solution and you need remote access only to on-premises web-based apps | You have configured Azure Application Proxy. |
| No remote access VPN solution and you need access to on-premises apps, some of which are not web-based | You have configured Azure P2S VPN. |
| Remote workers are using their personal devices from home | You have configured Windows Virtual Desktop. |
| Remote workers are using RDS connections to on-premises systems | You have deployed a Remote Desktop Services gateway in your edge network. |
Next step
Continue with Step 3 to deploy Microsoft 365 security and compliance services to protect your apps, data, and devices.
